Secure Serverless Azure Functions AppSetting Using Key Vault
[toc]
Introduction
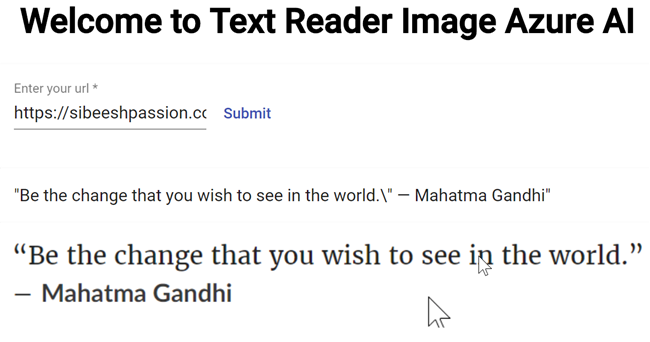
Security is something that we all are worried about, especially if your applications are in cloud. If someone is able to see the credentials or client’s data, then you lose the trust you have with your customer. I know, that no one likes it. Fortunately, every cloud providers have already provided enough options to make your application safe and secure. Here, in this post, we are going to discuss about such a feature in Microsoft Azure. I hope you have already used Azure Functions, if you have not, I strongly recommend you to see some related articles here. Here in this article, we will see how we can get the connection strings from Azure Key Vault and use it in our Azure Function instead of using it from the usual App Settings. Sounds interesting? So, let us do it.
Prerequisites
It would be great if are familiar with the preceding topics.
- Microsoft Azure
- Server less
- C#, or any other programming languages
You should have a valid Azure Subscription to follow along.
Background
As I was explaining, we are going to change the way we take the connection strings and other values in our Azure Function. Below is my Azure Function sample code.
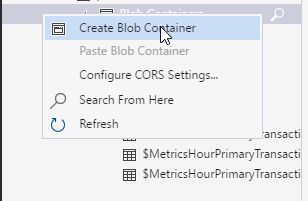
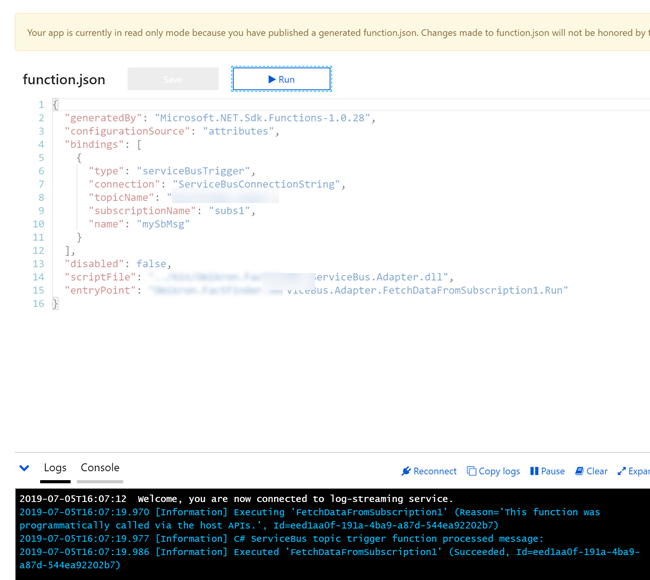
As you can see that this function has custom binding with my service bus as it uses ServiceBusTrigger. The connection string name is ServiceBusConnectionString which we have already set in the Azure Function configuration.
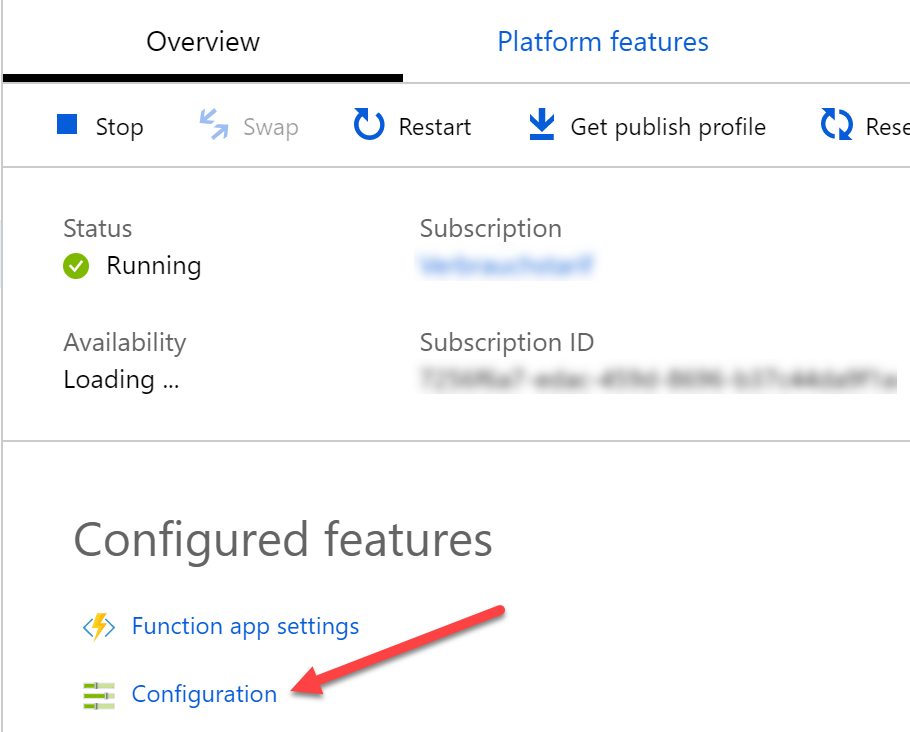
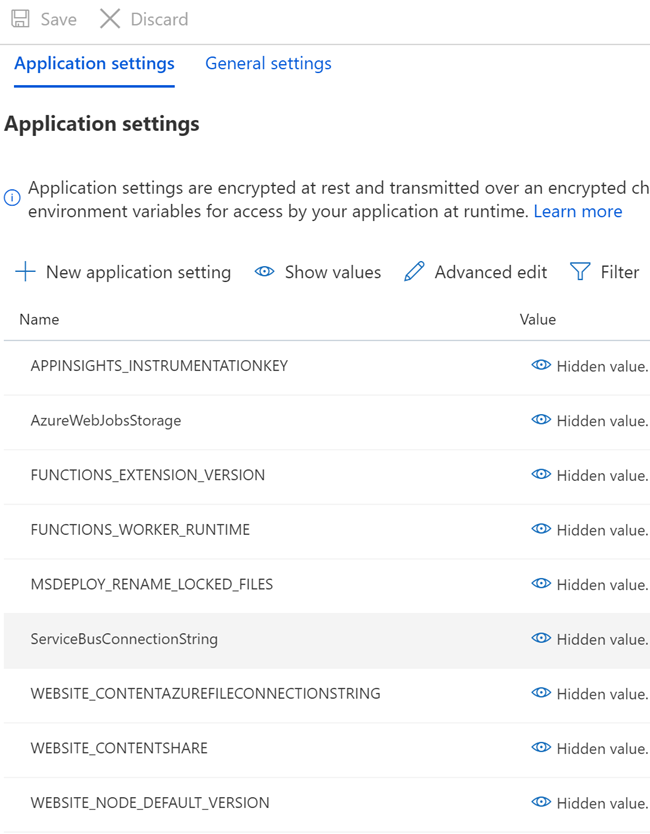
You should be able to see all of your configurations and application settings once you click on the configuration tab.
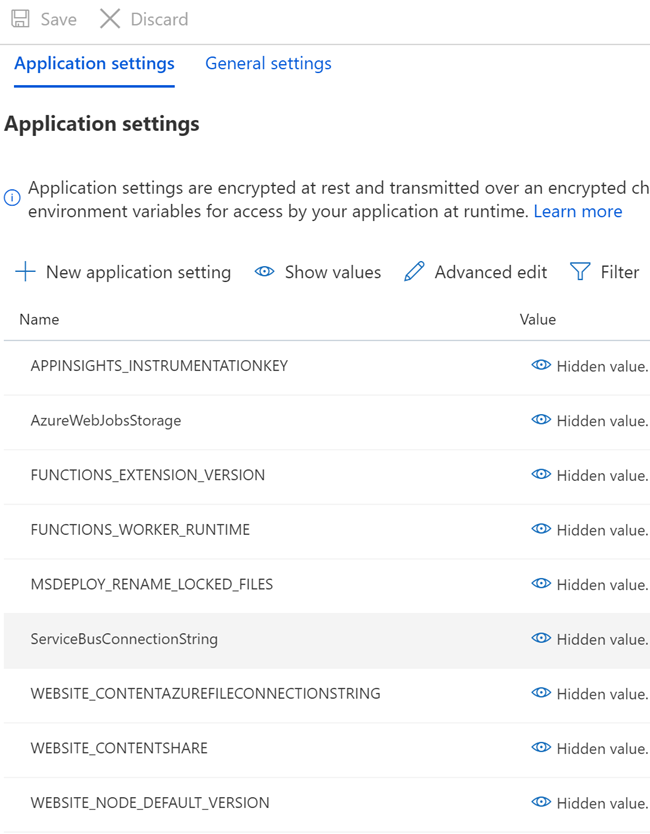
Here in this post, we are going to change the value of ServiceBusConnectionString to the AzureKey Vault reference. This connection string is given by the customer, isn’t it always better to make it as secured as possible?
Configure Azure Key Vault
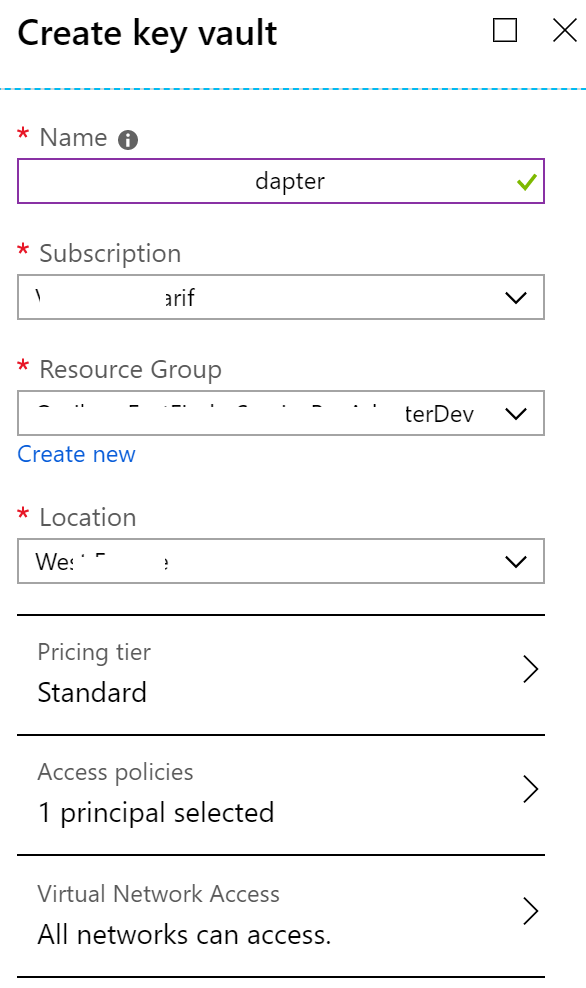
To get start, we should create an Azure Key Vault, please go to your Azure Portal and search with the keyword Key Vaults.
Once you had filled all the required information in the form, you can click on the create button.
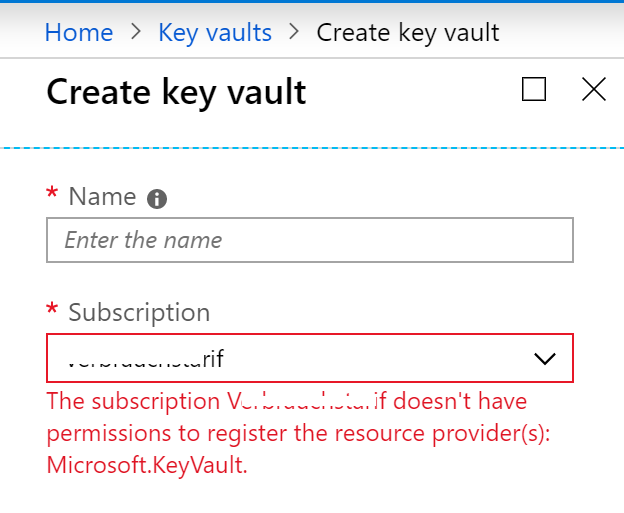
If you are getting an error as shown in the image below, you should go to the Resource Provider section of your Subscription and then search for Microsoft.KeyValut and then click on register.
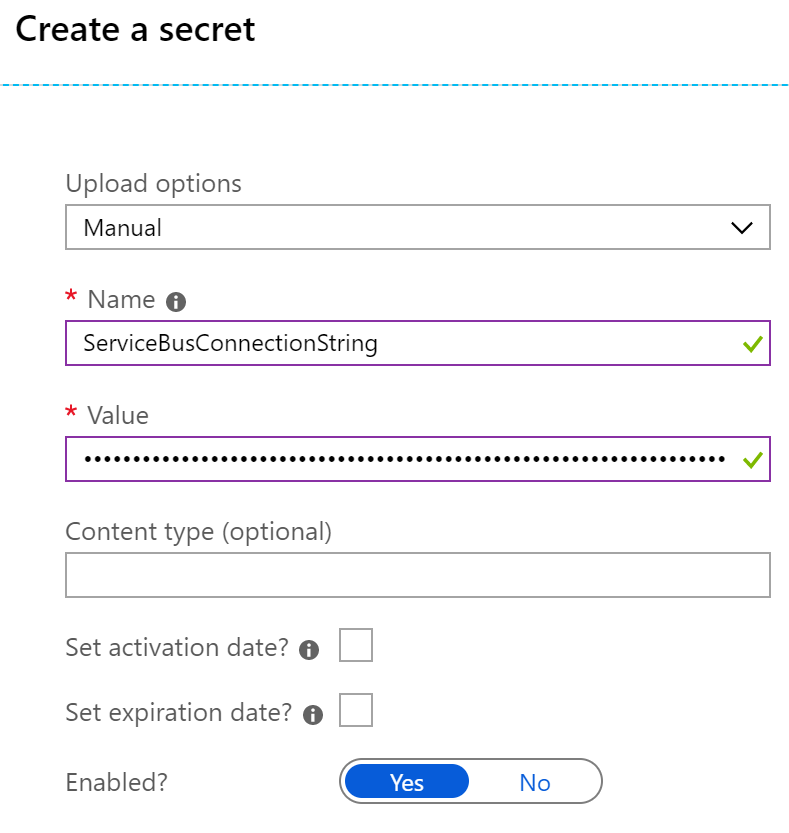
The key vault should be deployed in few seconds or minutes. Now you can go to your Key Vault. You can add Keys, Secrets, Certificates etc to your Key Vaults. But in this post, we are going to add a new Secret for our connection string. Click on the Secrets blade and then click on Generate/Import button. Now let us give all the details as shown in the below image.
Set Key Vault Access Policy
It is great that we have a Key Vault and secret, now we can give permission to our Azure Function application to retrieve this secrets from the Key Vault. But before you do that, you need to add a managed identity to the Azure Function.
Add a System Assigned Managed Identity to the Azure Function
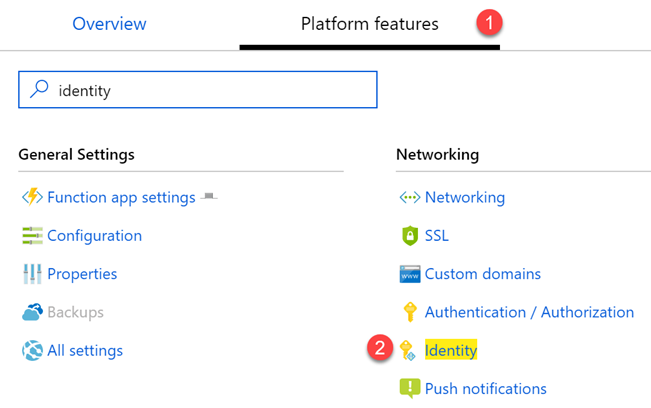
To create an identity, please go to the Platform Features of your Azure Function and click on Identity.
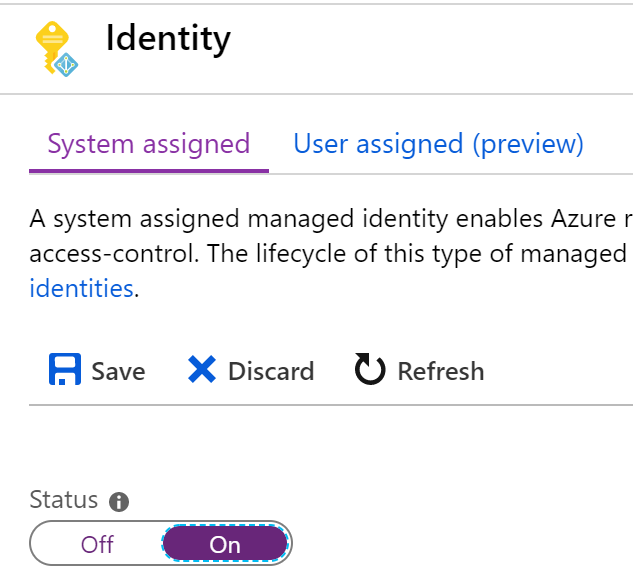
Now let’s enable the System Assigned Identity.
Add Access Control
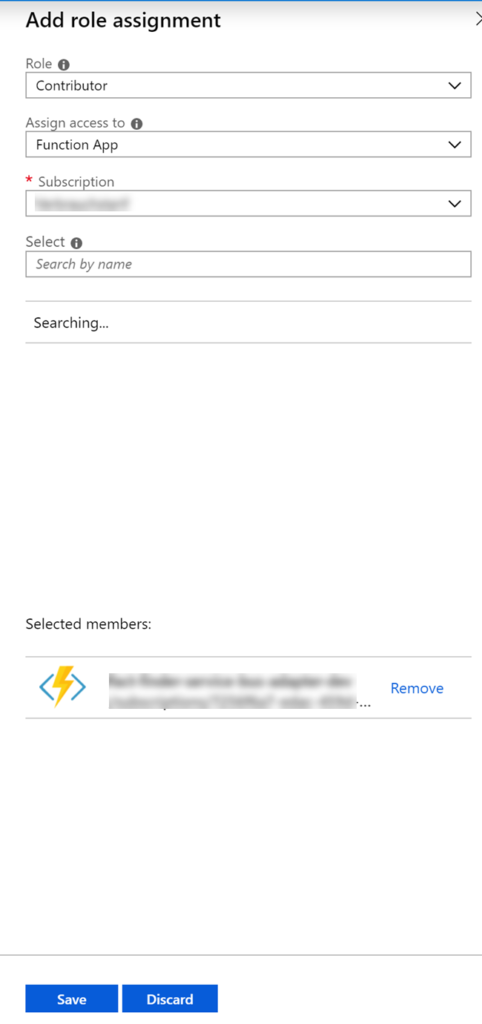
To give the access policy, first we should add a role assignment with contributor role for our application. Now we should also be able to add new role assignment. To do so, go to the Access Control section of your Key Vault and click on Add a role assignment blade.
Add Access Policy
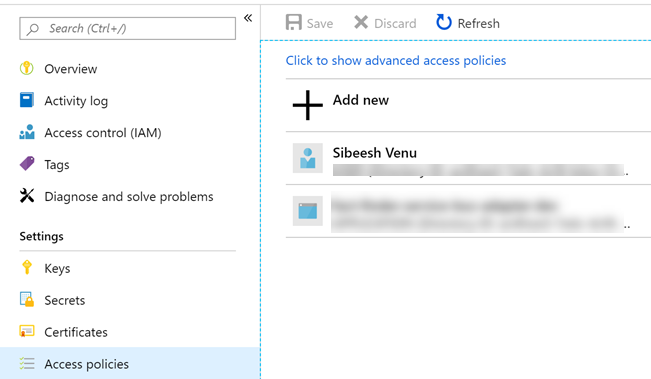
Now that we have created a managed identity and a role assignment, we should be able to add the Access Polity in the Key Vault for our Azure Function. Go to your Key Vault and click on Access Policies and then click on Add new blade.
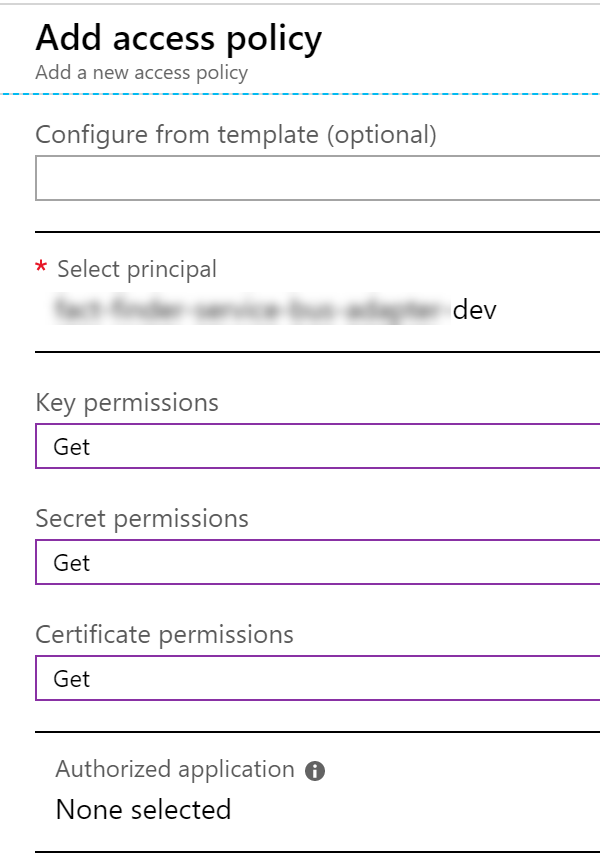
Please makes sure to use the, Object ID of the System Assigned Manged Identity that we have already created, here in the Select Principal column. This will make sure that our Azure Function has access to get the value from the Azure Key Vault.
At the end, you should have access policies as below.
Use the Key Vault Secret in Azure Function
Now that we have created our secret, and set up the access policy, we can get the secret identifier, to get this, please click on the secret you had created and then version. You should see a window as below.
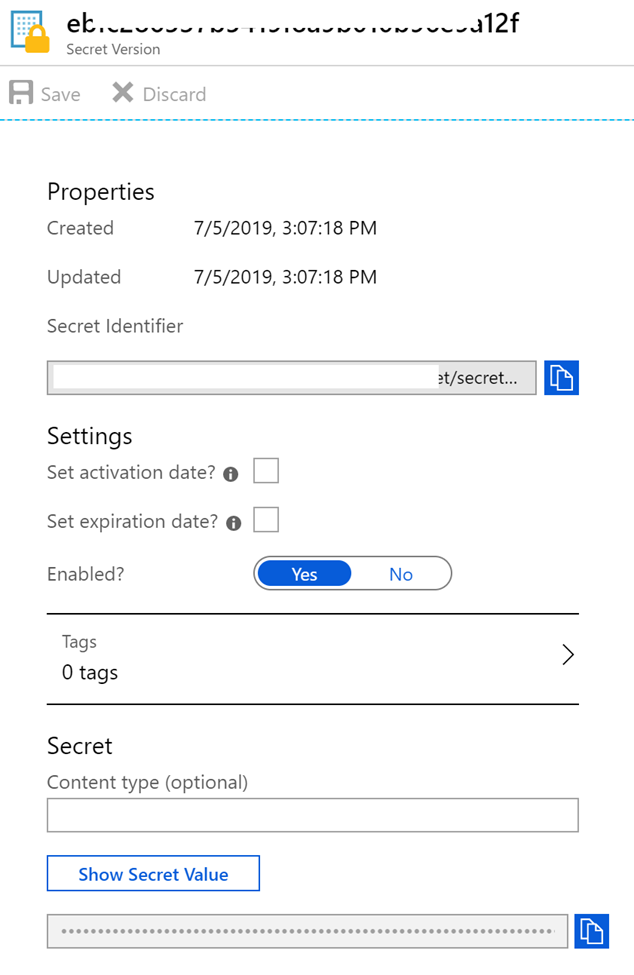
The good thing is you can even provide the activation date and the expiry date. Isn’t it handy? Copy the value and then go to the configuration page of your Azure Function and then click on the app settings that you want to change, in my case the app setting with the key ServiceBusConnectionString. Now, you should see an option to edit the value there. Now you can give the value there as below.
@Microsoft.KeyVault(SecretUri=Secret URI with version)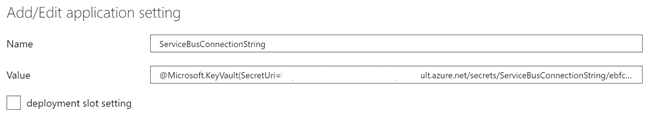
Remember to save the changes and you get the notification as ” Successfully updated web app settings “. That’s it. Now you should be able to run your Azure Functions, the only difference is that we are getting the app settings value from the Key Vault.
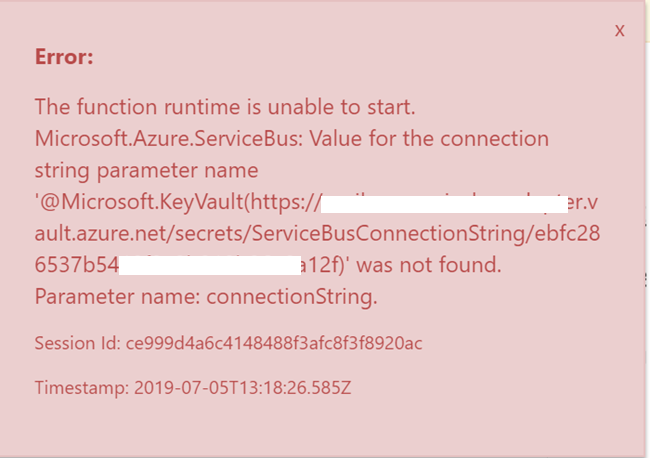
By chance if you get an error as “The function runtime is unable to start. Microsoft.Azure.ServiceBus: Value for the connection string parameter name ‘@Microsoft.KeyVault“, please make sure that the right format @Microsoft.KeyVault(SecretUri=Secret URI with version) in the Value column.
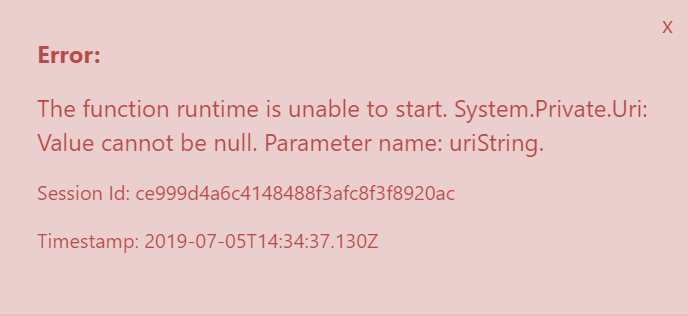
Or if you get any error as “Value can not be null. Parameter name: uriString“, please make sure that you have done the Access Policy configuration correctly.
Run Azure Function
Now you can go to your Azure Functions and try to run any one of them which uses the app settings that we have configured. If everything is fine, you should be able to run the Function and should get some responses.
Conclusion
In this article, we have learned,
- About Azure Function and it’s configuration
- How to configure Azure Key Vault
- How to set Managed Identity for an Azure Function application
- How to create Role Assignments in Key Vault Access Control
- How to create Access policies for the managed identity
- How to use Azure Key vault secret in the Azure Function app settings
Please let me know what else you had learned from this Article.
Your turn. What do you think?
Thanks a lot for reading. Did I miss anything that you may think which is needed in this article? Could you find this post as useful? Kindly do not forget to share me your feedback.
Kindest Regards
Sibeesh Venu